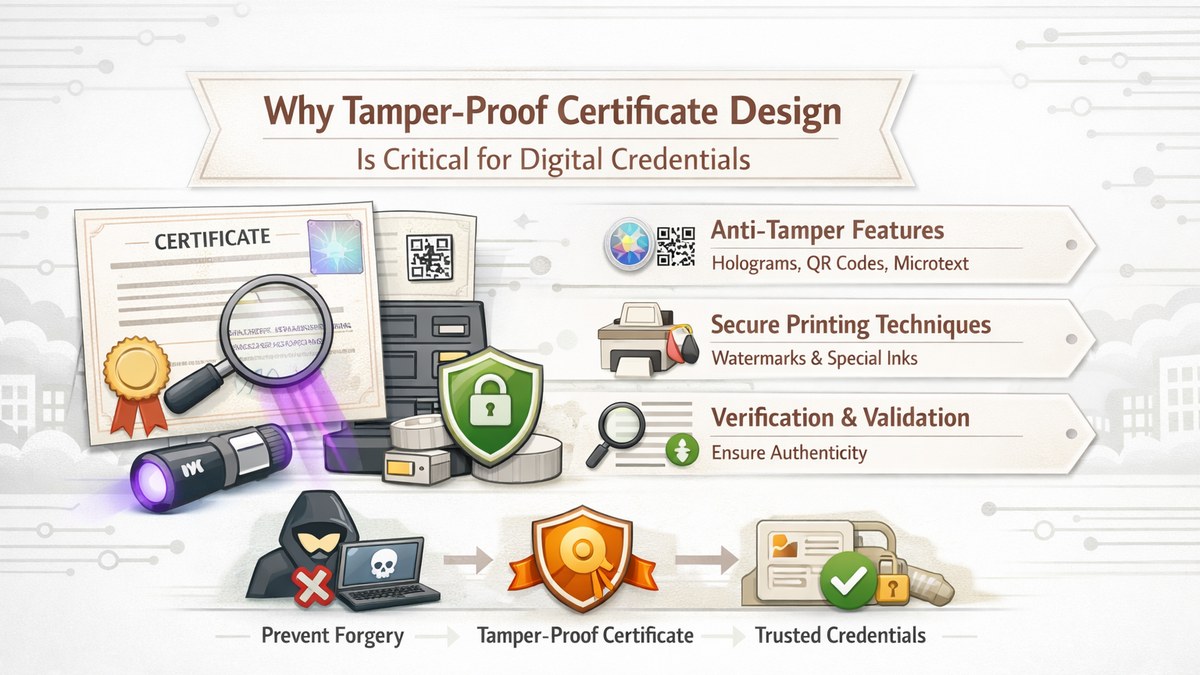
Why Tamper-Proof Certificate Design Is Critical for Digital Credentials
The transition from paper-based certification to digital credentialing has introduced new efficiencies, scalability, and accessibility. However, it has also created new vulnerabilities. Unlike physical certificates, which are relatively difficult to alter without detection, digital certificates can be copied, edited, and redistributed with minimal effort if adequate safeguards are not implemented. As a result, tamper-proof certificate design has become a foundational requirement in modern credential systems.
In any credentialing framework, the value of a certificate is directly tied to its integrity. A certificate that can be easily modified or replicated undermines the trust placed in both the credential and the issuing institution. Therefore, ensuring that certificates are resistant to unauthorized modification is essential for maintaining long-term credibility and institutional reputation.
Understanding Tamper-Proof Certificate Design
A tamper-proof certificate is one in which unauthorized alterations are either technically prevented or rendered immediately detectable. This is achieved not through a single mechanism, but through a combination of design principles, system architecture, and validation frameworks. The objective is to ensure that any deviation from the original, authoritative record can be identified with certainty.
This approach aligns with broader principles of secure digital systems, where data integrity, traceability, and verifiability are prioritized throughout the lifecycle of a digital artifact [1].
Core Risks in the Absence of Tamper Protection
Without tamper-resistant mechanisms, digital certificates are vulnerable to multiple forms of misuse, each of which can have significant consequences.
1. Unauthorized Data Modification
Certificate fields such as recipient names, dates, or qualifications can be altered using basic editing tools. Such modifications can result in false claims of participation, achievement, or certification.
2. Duplication and Identity Misrepresentation
A single certificate file may be duplicated and reused across multiple individuals. Without embedded uniqueness or verification capability, distinguishing between legitimate and fraudulent copies becomes difficult.
3. Erosion of Institutional Trust
The circulation of altered or counterfeit certificates can significantly damage the credibility of the issuing organization. Over time, this may lead to increased verification burdens and reduced acceptance of credentials.
Architectural Principles for Tamper Resistance
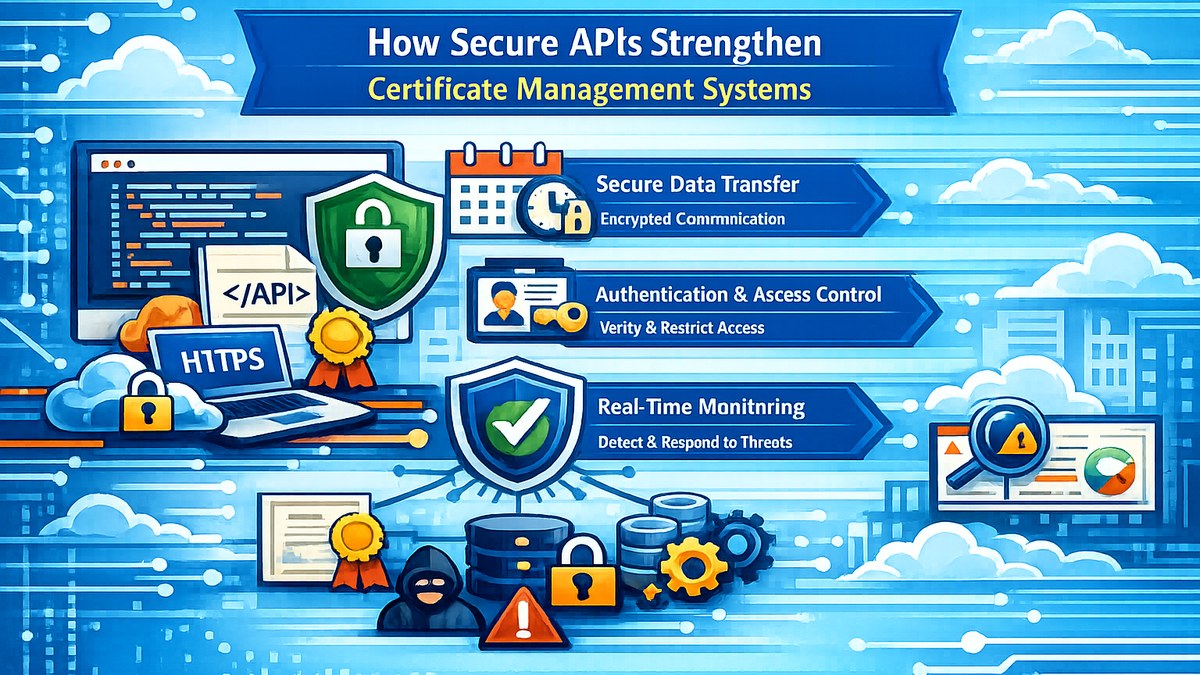
Effective tamper-proof design relies on a layered security model, where multiple mechanisms work together to protect certificate integrity.
1. Unique Certificate Identifiers
Each certificate should be associated with a globally unique identifier that links it to a specific record within the issuing system. This identifier acts as a reference point for validation and traceability.
2. QR-Based and Link-Based Verification
Embedding QR codes or secure verification links enables third parties to validate certificates against an authoritative source. This ensures that even if a certificate is modified, discrepancies can be detected during verification.
3. Server-Side Rendering and Data Binding
Certificates generated through server-side processes ensure that all content is derived from validated backend data. This minimizes the risk of client-side manipulation and enforces consistency across outputs.
4. Controlled Access and Distribution
Secure delivery mechanisms such as token-based access or OTP verification reduce the likelihood of unauthorized distribution and misuse of certificate files.
5. Continuous Validation Frameworks
Tamper-proof systems extend beyond issuance by maintaining an ongoing validation capability. Certificates remain linked to a live verification system, ensuring their authenticity can be confirmed at any point in time.
Integration with Verification Ecosystems
Tamper-proof certificate design is most effective when integrated with broader verification ecosystems. This includes validation portals, audit logs, and revocation mechanisms. Such integration ensures that certificates are not treated as static documents but as dynamic, verifiable credentials connected to institutional records.
In large-scale deployments—such as universities, certification bodies, and professional organizations—this interconnected approach enhances both operational efficiency and trust.
Operational and Governance Considerations
From an institutional standpoint, tamper-proof design supports stronger governance by enabling traceability, auditability, and lifecycle management. Administrators can monitor certificate issuance, track validation requests, and respond to discrepancies in a structured manner.
This capability is particularly important in environments where compliance, accreditation, or regulatory oversight plays a significant role.
Conclusion
Tamper-proof certificate design is not merely a technical enhancement; it is a fundamental requirement for establishing and maintaining trust in digital credential systems. By combining secure rendering, unique identification, controlled distribution, and continuous verification, institutions can ensure that their certificates remain credible, verifiable, and resistant to misuse.
As digital credentials continue to gain widespread adoption across academic, professional, and organizational contexts, tamper-proof design will remain a cornerstone of secure and reliable credentialing frameworks.
References (Indicative)
[1] Data Integrity and Secure Design Principles in Digital Credential Systems
[2] Emerging Practices in Digital Certification and Verification Frameworks