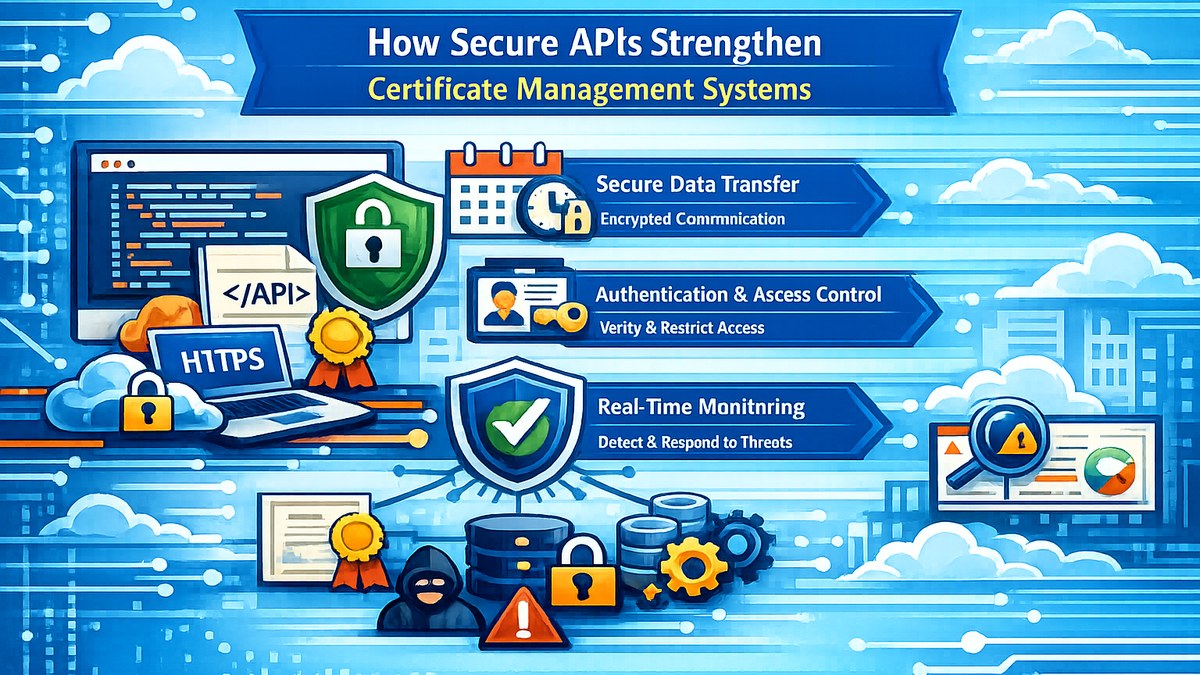
How Secure APIs Strengthen Certificate Management Systems
The evolution of digital certificate management systems has increasingly relied on integration across multiple platforms, including enterprise resource planning (ERP) systems, learning management systems (LMS), event platforms, and third-party verification services. At the center of this interconnected architecture are Application Programming Interfaces (APIs), which enable seamless data exchange and automation. However, while APIs enhance scalability and efficiency, they also introduce critical security considerations that must be carefully managed.
Secure APIs are therefore essential for ensuring that certificate data remains protected, accurate, and accessible only to authorized systems. In the absence of robust API security, certificate management systems may become vulnerable to unauthorized access, data leakage, and manipulation—undermining the integrity of digital credentials.
The Role of APIs in Certificate Ecosystems
APIs act as the communication layer between different components of a certificate ecosystem. They facilitate operations such as participant data ingestion, certificate generation triggers, verification requests, and integration with external platforms. By enabling automation, APIs significantly reduce manual effort and improve operational efficiency.
However, this central role also makes APIs a high-value target for potential security threats. Any vulnerability in API design or implementation can expose sensitive certificate data or allow unauthorized actions within the system.
Security Risks in Unprotected API Architectures
Without adequate safeguards, APIs can introduce multiple vulnerabilities that compromise both system integrity and institutional trust.
1. Unauthorized Access
Weak or absent authentication mechanisms may allow unauthorized entities to access certificate data, including personal information and credential details.
2. Data Manipulation
Insecure endpoints can enable attackers to alter certificate-related data, potentially leading to fraudulent credential generation or modification.
3. Excessive Data Exposure
Poorly designed APIs may return more data than necessary, increasing the risk of unintended information disclosure.
4. Abuse Through Automated Requests
Without proper rate limiting, APIs can be exploited through high-volume requests, leading to denial-of-service conditions or system instability.
Core Principles of Secure API Design
To mitigate these risks, certificate management systems must adopt a comprehensive approach to API security, incorporating multiple layers of protection.
1. Strong Authentication and Authorization
APIs should implement robust authentication mechanisms such as API keys, OAuth tokens, or signed requests. Role-based access control ensures that only authorized systems and users can perform specific actions.
2. Input Validation and Data Sanitization
All incoming data should be rigorously validated to prevent injection attacks and ensure that only well-formed, expected inputs are processed.
3. Rate Limiting and Throttling
Implementing request limits helps prevent abuse and ensures system stability under varying loads.
4. Encryption and Secure Communication
All API communication should occur over encrypted channels (such as HTTPS) to protect data in transit from interception or tampering.
5. Minimal Data Exposure
APIs should follow the principle of least privilege, returning only the data necessary for a specific operation.
Integration with Certificate Security Frameworks
Secure APIs do not operate in isolation; they form a critical component of the broader certificate security framework. When properly implemented, APIs integrate seamlessly with server-side rendering engines, verification systems, audit logs, and access control mechanisms.
This integration ensures that certificate data remains consistent across all stages—from issuance to validation—while maintaining strict control over how data is accessed and modified.
Operational and Governance Benefits
From an institutional perspective, secure APIs enable scalable and controlled automation. Organizations can integrate certificate systems with external platforms without compromising security. Additionally, API activity can be logged and monitored, providing valuable insights for auditing, compliance, and anomaly detection.
Such capabilities are particularly important in large-scale deployments where certificate systems serve thousands of users across multiple programs or events.
Conclusion
Secure APIs are a foundational element of modern certificate management systems. By enabling safe integration, protecting sensitive data, and enforcing controlled access, they ensure that digital credentials remain trustworthy and resilient. As certificate ecosystems continue to expand and integrate with external platforms, the importance of robust API security will only increase.
References (Indicative)
[1] API Security Best Practices in Distributed Systems
[2] Secure Integration Frameworks for Digital Credential Platforms