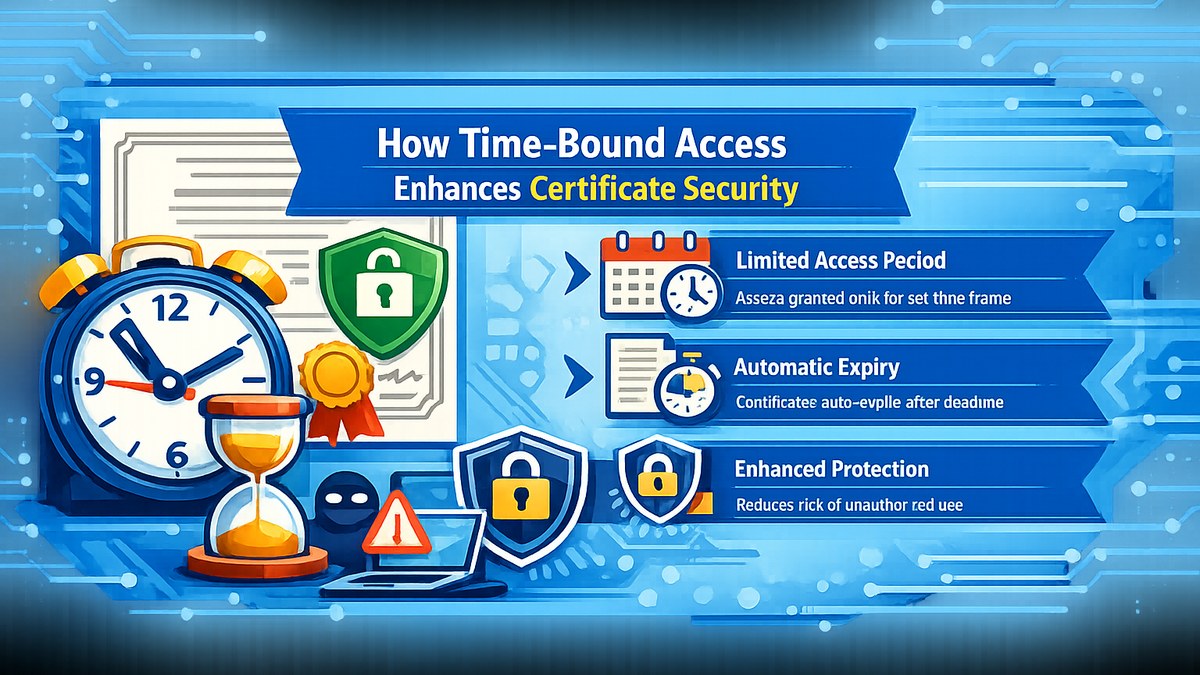
How Time-Bound Access Enhances Certificate Security
In digital certificate systems, access control is not just about who can access a certificate, but also when it can be accessed. Time-bound access adds an important layer of protection by limiting the validity period of links or tokens.
This ensures that even if a link is shared or exposed unintentionally, it cannot be used indefinitely.
Why Time-Bound Access Is Important
Permanent access links increase the risk of unauthorized distribution. Time-bound access reduces this risk by automatically expiring access after a defined period.
Benefits
1. Reduced Misuse
Expired links cannot be reused or exploited.
2. Better Control
Organizations can define access windows aligned with event timelines.
3. Enhanced Security
Temporary access reduces exposure to potential threats.
Implementation Approaches
Time-bound access is commonly implemented using expiring tokens, session validation, or OTP-based authentication flows.
Conclusion
Time-bound access adds a simple yet powerful layer of security, ensuring that certificate systems remain controlled, secure, and aligned with best practices.