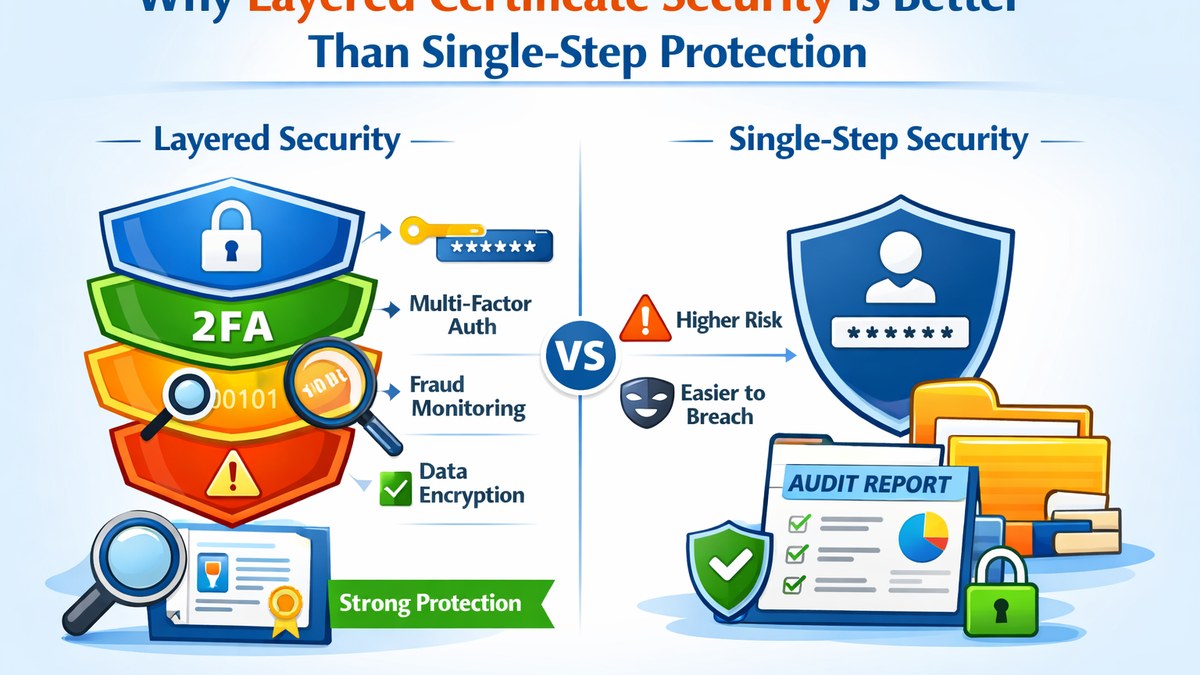
Why Layered Certificate Security Is Better Than Single-Step Protection
Digital certificate security works best when it is built in layers. Relying on only one protection method, such as a download link or a single access check, may reduce some risk, but it does not create a complete trust framework. This is why layered certificate security is the better approach.
A strong certificate system combines controlled access, structured records, verification support, and distinct certificate identity into one dependable workflow.
What Layered Security Means
Layered security means using multiple protective measures together rather than depending on a single gate. In digital credential systems, this may include secure access flows, unique certificate IDs, QR-based verification, trusted verification pages, and structured event-linked records.
Why a Single Layer Is Not Enough
A certificate may be accessed securely but still lack strong verification support. Or it may have a QR code but weak record structure behind it. Each measure helps, but the system becomes significantly stronger when these measures reinforce each other.
Benefits of Layered Certificate Security
1. Better Protection Across the Full Lifecycle
Security applies not only during download but also during sharing, verification, and long-term retrieval.
2. Better Trust for External Reviewers
When multiple validation cues exist, the credential feels more dependable.
3. Better Operational Resilience
If one layer is limited in a particular scenario, other layers still reinforce the system.
4. Better Institutional Credibility
Organizations that use layered protection signal greater seriousness about credential integrity.
Why This Approach Works Best
Security is strongest when it is not treated as a single feature but as an overall design principle. Layered systems protect the certificate as a digital asset, support the recipient more effectively, and reduce uncertainty for institutions and reviewers.
Conclusion
Layered certificate security provides a stronger, more trustworthy foundation than any single-step protection method alone. For modern digital credential systems, it is the most practical way to combine usability, verification, and institutional confidence.